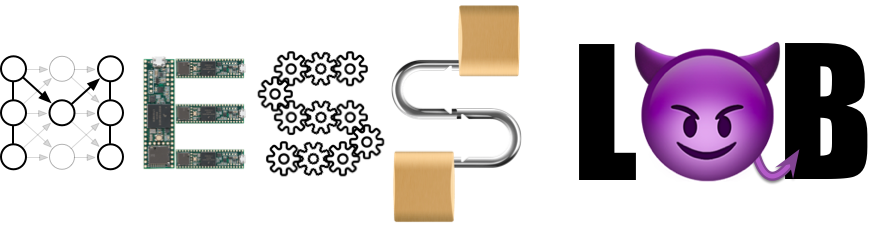
The MESS Lab is a security lab at the NYU Tandon School of Engineering. Our research focuses on Machine Learning, Embedded Systems, and Software/Systems Security. The MESS Lab is part of the NYU Center for Cybersecurity.
News
November 17, 2022 Our paper on fine-tuning code models for Verilog, Benchmarking Large Language Models for Automated Verilog RTL Code Generation, has been accepted at DATE 2023 and nominated as Best Paper Award Candidate! Preprint coming soon! :)
November 9, 2022 Prof. BDG appeared on stage at GitHub Universe to discuss Copilot security with Eirini Kalliamvakou and Ryan Salva during the session A backstage pass with GitHub Copilot.
October 12, 2022 Our research on the security of GitHub Copilot was mentioned by Microsoft CEO Satya Nadella during his Microsoft Ignite keynote!
August 8, 2022 Examining Zero-Shot Vulnerability Repair with Large Language Models has been accepted at the IEEE Symposium on Security and Privacy 2023! This paper evaluates the performance of large language models trained on code (e.g., OpenAI Codex) at automatically fixing vulnerabilities in software.
May 3, 2022 Drifuzz: Harvesting Bugs in Device Drivers from Golden Seeds by Zekun Shen, Ritik Roongta, and Brendan Dolan-Gavitt has been accepted for publication at USENIX Security 2022! This work focuses on finding good seeds for fuzzing complex PCI and USB WiFi and Ethernet drivers, and found eleven previously unknown bugs in Linux kernel device drivers, with two CVEs assigned (CVE-2021-43975 and CVE-2021-43976).
Apr 28, 2022 Our paper on detecting malware in GitHub forks, What the Fork? Finding and Analyzing Malware in GitHub Forks, won best paper runner up at MADWeb. Congratulations to Alan Cao!
Feb 21, 2022 The MESS Lab will have two papers at NDSS workshops this year! Stay tuned for more details and preprints of Beyond the C: Retargetable Decompilation using Neural Machine Translation by Iman Hosseini and Brendan Dolan-Gavitt (NDSS Binary Analysis Research Workshop), and What the Fork? Finding and Analyzing Malware in GitHub Forks by Alan Cao and Brendan Dolan-Gavitt at MADWeb. Congratulations to Iman and Alan!
Jan 25, 2022 Prof. Dolan-Gavitt has received an NSF CAREER award to support the MESS Lab’s research into improved techniques for automatically generating large, diverse, and realistic benchmarks of software vulnerabilities. The five-year project, Generating High Quality Vulnerability Corpora for Benchmarking and Education, will extend and improve on LAVA and use large language models trained on real code and vulnerabilities to create realistic flaws that can be used to evaluate vulnerability discovery tools and automatically create CTF-style challenges for training and education.
Dec 21, 2021 Congratulations to Yu Hu and Zekun Shen on having their paper, Characterizing and Improving Bug-Finders with Synthetic Bugs accepted at the IEEE International Conference on Software Analysis, Evolution and Reengineering (SANER)!
Nov 6, 2021 MESS Lab members had two papers accepted at the IEEE Symposium on Security and Privacy (S&P/Oakland)! IRQDebloat: Reducing Driver Attack Surface in Embedded Devices by Zhenghao Hu and Brendan Dolan-Gavitt and Asleep at the Keyboard? Assessing the Security of GitHub Copilot’s Code Contributions by Hammond Pearce, Baleegh Ahmad, Benjamin Tan, Brendan Dolan-Gavitt, and Ramesh Karri will be presented at the conference in May 2022. Congrats to everyone involved, particularly Baleegh and Zhenghao for their first Oakland papers!
Oct 6, 2021 We ran ChaffCTF, a small capture the flag (CTF) competition based around Chaff Bugs! Zhenghao Hu did a writeup about how the ChaffCTF challenges were created and how to solve them.